TSS-WEB - an Open Framework for your Web Development Security Policy or Standard
This is the official site of TSS-WEB, an open framework of ~200 baseline requirements that you can use for your web development security standard, policy, or security concept. All of these requirements are based on common best practices (including those from OWASP, SAFECode, ISO/IEC 27002, NIST and BSI) plus our own experiences in this field.
For instance, TSS-WEB also meets 14.2.1 control ("Secure Development Policy") of ISO/IEC 27002. Detailed compliance mappings are provided in appendix B to E.
Deprecated
This version of TSS-WEB is now depracted. You'll find the current one at https://tss-web.secodis.com/.
Objective
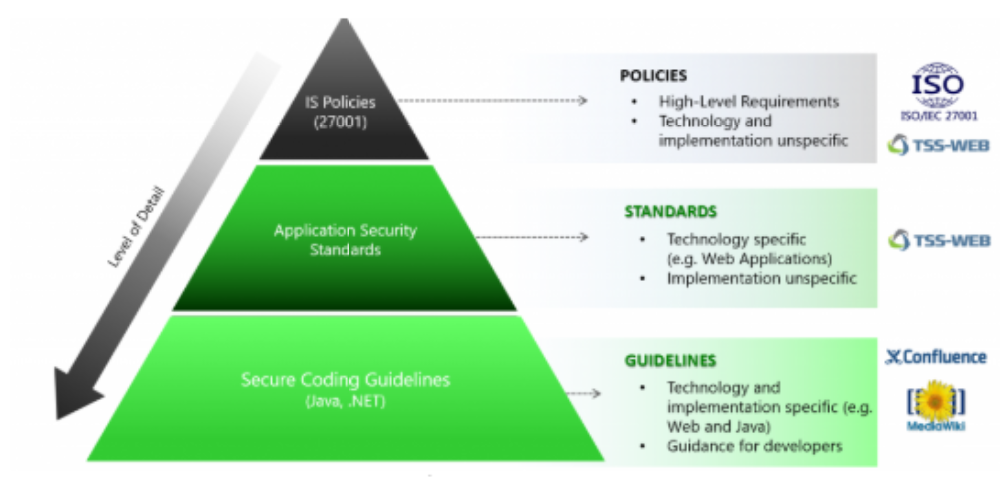
The objective of TSS-WEB is to provide a framework of language-independent application security requirements that can be used by organizations as a baseline to implement their own security standards or policies for their web development.
Secure Coding Guidelines
TSS-WEB provides high-level requirements that can be used to derive secure coding guidelines for specific languages and frameworks.
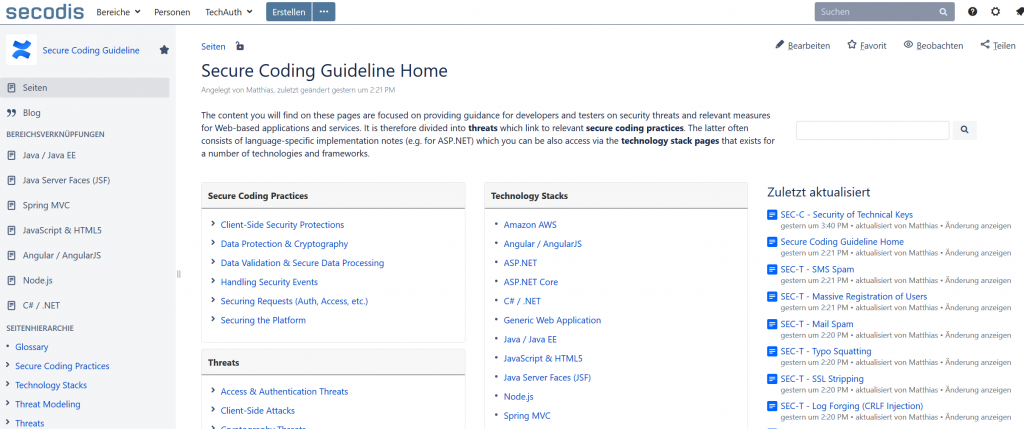
Secure Coding Guidelines for Confluence by Secodis
If you are interested in comprehensive secure coding guidelines that complement these requirements, you might want to have a look at our Security Guidelines for Confluence that we provide as an export for Atlassian Confluence. It includes a comprehensive threat library, secure coding guidelines, and implementation notes for a number of programming languages and frameworks including Java, JSF, Spring, ASP.NET, Angular, Javascript, and Node.js that you can extend to your own need or that we update for you on a regular basis. Here is what it looks like:
Related Standards
ISO/IEC 27002:2013: Appendix E: ISO/IEC 27002:2013 Mapping (Draft)
- OWASP SAMM 2.0 (Maturity Model): Appendix D: OWASP SAMM 2.0 Mapping
- BSIMM (Maturity Model)
- IT-Grundschutz-Kompendium 2020 (German Standard): Appendix C: BSI Grundschutz Mapping (German)
- SAFECode Software Integrity Controls
- NIST Secure Software Development Framework (SSDF)
- OWASP Top Ten 2017 (only implementation requirements): Appendix B: OWASP Top Ten 2017 Mapping
License
The document is licensed under Creative Commons By 4.0 and can therefore be used and changed to individual needs free of charge and without any other obligations than to name the document and author of the used template. Furthermore, any adapted version of this document does not have to be published under the same license.
Author
This site is maintained by Secodis GmbH. Responsible for the content is Matthias Rohr.
Downloads
English:
German:
Search
Table of Contents
- 1. Introduction
- 2. Remediation of Vulnerabilities in Production
- 3. Secure Operation
- 4. Secure Development Environment
- 5. Security within Software Development Process
- 6. Security Tests
- 7. Outsourced Development
- 8. Implementation Requirements
- Appendix A: Requirements for HTTP Security Header
- Appendix B: OWASP Top Ten 2017 Mapping
- Appendix C: BSI Grundschutz Mapping (German)
- Appendix D: OWASP SAMM 2.0 Mapping
- Appendix E: ISO/IEC 27002:2013 Mapping (Draft)
Updates since v1.8
Relevant changes since v1.8:
-
8.1 General Design PrinciplesJul 12, 2024 • contributed by Matthias Rohr
-
Appendix A: Requirements for HTTP Security HeaderFeb 24, 2023 • contributed by Matthias Rohr
-
5. Security within Software Development ProcessMay 21, 2021 • contributed by Matthias Rohr
-
3. Secure OperationFeb 10, 2021 • contributed by Matthias Rohr
-
8.6 User PasswordsJan 13, 2021 • contributed by Matthias Rohr
-
8.13 Service & API SecurityJan 12, 2021 • contributed by Matthias Rohr
-
8.12 Client-Side SecurityJan 12, 2021 • contributed by Matthias Rohr
-
8.11 Protection of SecretsJan 12, 2021 • contributed by Matthias Rohr
-
8.10 Data Security & CryptographyJan 12, 2021 • contributed by Matthias Rohr
-
6. Security TestsJan 12, 2021 • contributed by Matthias Rohr
-
8.9 Error Handling & LoggingJan 12, 2021 • contributed by Matthias Rohr
-
8.8 Access ControlsJan 12, 2021 • contributed by Matthias Rohr
-
8.7 Hardening of Session ManagementJan 12, 2021 • contributed by Matthias Rohr
-
8.3 File Uploads and DownloadsJan 12, 2021 • contributed by Matthias Rohr
-
8.2 Input ValidationJan 12, 2021 • contributed by Matthias Rohr